5 05 2015
Microsoft 70-642 Practice Questions Free Download From Braindump2go (171-180)
Braindump2go Updates Microsoft 70-642 Exam Dumps Questions, adds some new changed questions from Microsoft Official Exam Center. Want to know 2015 70-642 Exam test points? Download the following free Braindump2go Latest Exam Questions Today!
Vendor: Microsoft
Exam Code: 70-642
Exam Name: TS: Windows Server 2008 Network Infrastructure, Configuring
Keywords: 70-642 Exam Dumps,70-642 Practice Tests,70-642 Practice Exams,70-642 Exam Questions,70-642 Dumps,70-642 PDF,70-642 VCE,70-642 Study Guide
QUESTION 171
Your company has a single Active Directory forest that has a domain in North America named na.contoso.com and a domain in South America named sa.contoso.com.
The client computers run Windows 7.
You need to configure the client computers in the North America office to improve the name resolution response time for resources in the South America office.
What should you do?
A. Configure a new Group Policy object (GPO) that disables the Local-Link Multicast Name
Resolution feature.
Apply the policy to all the client computers in the North America office.
B. Configure a new Group Policy object (GPO) that enables the Local-Link Multicast Name
Resolution feature.
Apply the policy to all the client computers in the North America office.
C. Configure a new Group Policy object (GPO) that configures the DNS Suffix Search List
option to sa.contoso.com, na.contoso.com.
Apply the policy to all the client computers in the North America office.
D. Configure the priority value for the Service Location (SRV) records on each of the North
America domain controllers to 5.
Answer: C
QUESTION 172
Your network contains an Active Directory domain named fabrikam.com.
The domain contains five domain controllers named DC1, DC2, DC3, DC4, and DC5.
All domain controllers run Windows Server 2008 R2 and have the DNS server role installed.
On DC5, you create a new Active Directory-integrated DNS zone named adatum.com.
You need to ensure that the adatum.com DNS zone is only replicated to DC5 and DC2.
The solution must ensure that all zone replication traffic is encrypted.
What should you do first?
A. Create an application directory partition.
B. Create a primary zone.
C. Modify the zone transfer settings.
D. Change the zone replication scope.
Answer: A
QUESTION 173
Your network contains a server named Server1 that runs Windows Server 2008 R2.
You enable IPSec on Server1.
You need to identify which client computers have active IPSec associations to Server1.
Which administrative tool should you use to achieve this task? To answer, select the appropriate tool from the answer area.
![173_thumb[1] 173_thumb[1]](http://examgod.com/bdimages/16b1e32bb31d_7AEA/173_thumb1_thumb.jpg)
Answer:
![173-1_thumb[1] 173-1_thumb[1]](http://examgod.com/bdimages/16b1e32bb31d_7AEA/173-1_thumb1_thumb.jpg)
QUESTION 174
Your network contains a server named Server1 that runs Windows Server 2008 R2.
On Server1, you run route add 192.168.10.0 mask 255.255.255.0 172.23.1.2 metric 10.
You restart Server1, and then run the route command as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that after you restart Server1, Server1 routes all of the traffic for 192.168.10.0/24 by using the router that has an IP address of 172.23.1.2.
Which command should you run on Server1?
![174_thumb[2] 174_thumb[2]](http://examgod.com/bdimages/16b1e32bb31d_7AEA/174_thumb2_thumb.jpg)
A. netstat -p ip 172.23.1.2
B. netstat -f 172.23.1.2
C. route add 192.168.10.0 mask 255.255.255.0 172.23.1.2 metric 10 -p
D. route add 192.168.10.0 mask 255.255.255.128 172.23.1.2 metric 1 -f
Answer: C
QUESTION 175
Your company has 10 servers that run Windows Server 2008 R2.
The servers have Remote Desktop Protocol (RDP) enabled for server administration.
RDP is configured to use default security settings.
All administrators’ computers run Windows 7.
You need to ensure the RDP connections are as secure as possible.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Set the security layer for each server to the RDP Security Layer.
B. Configure the firewall on each server to block port 3389.
C. Acquire user certificates from the internal certification authority.
D. Configure each server to allow connections only to Remote Desktop client computers that
use Network Level Authentication.
Answer: CD
QUESTION 176
Your network contains a server that runs Windows Server 2008 R2 named Server1.
You install a new application on Server1.
After the installation, you discover that Server1 frequently becomes unavailable.
You need to identify whether the issues on Server1 coincide with the installation of the application.
What should you do?
A. From Reliability Monitor, review the reliability details.
B. From Administrative Tools, run Windows Memory Diagnostic.
C. From the System Configuration utility, select Diagnostic startup.
D. From the command prompt, run the Program Compatibility Wizard.
Answer: A
Explanation:
Reliability Monitor maintains up to a year of history for system stability and reliability events.
The System Stability Chart displays a rolling graph organized by date.
The top half of the System Stability Chart displays a graph of the Stability Index.
In the lower half of the chart, five rows track Reliability Events that either contribute to the stability measurement for the system or provide related information about software installation and removal.
When one or more Reliability Events of each type are detected, an icon appears in the column for that date.
For Software Installs and Uninstalls, an Information icon indicates a successful event of that type occurred, or a Warning icon indicates a failure of that type occurred.
For all other Reliability Event types, an Error icon indicates a failure of that type occurred.
http://technet.microsoft.com/en-us/library/cc749583(v=ws.10).aspx
QUESTION 177
Your network contains a file server named Server1 that runs Windows Server 2008 R2.
Users report that when they try to open some of the folders in \\server1\folder1, they receive an Access is Denied error message.
You need to ensure that when the users connect to \\server1\folder1, they only see the files and the folders to which they are assigned permissions.
Which tool should you use?
A. Local Security Policy
B. Share and Storage Management
C. Windows Explorer
D. Windows Firewall with Advanced Security
Answer: B
Explanation:
http://technet.microsoft.com/fr-fr/library/dd772681(v=ws.10).aspx
Access-based enumeration displays only the files and folders that a user has permissions to access. Accessbased enumeration is now included in the Windows Server 2008 operating system, and you can enable it by using Share and Storage Management.
QUESTION 178
Your network contains an Active Directory domain named contoso.com.
All server run Windows Server 2008 R2.
The topology of the Active Directory site is configured as shown in the exhibit. (Click the Exhibit button.)
Server1 and Server2 host a Distributed File System (DFS) replica named \\contoso.com\dfs\Folder1 .
You discover that client computers in Site3 and Site4 always contact Server1 when they access files in \\contoso.com\dfs\Folder1.
You need to ensure that client traffic from Site3 and Site4 is distributed between Server1 and Server2.
What should you do?
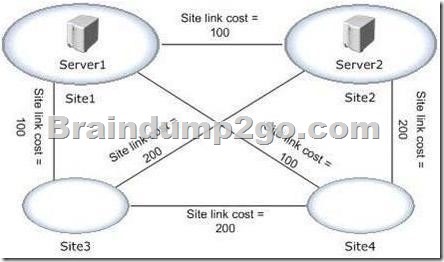
A. From the properties of the \\contoso.com\dfs\folder1 folder, modify the referrals settings.
B. From the properties of the \\contoso.com\dfs\folder1 folder, modify the advanced settings.
C. From the properties of the \\contoso.com\dfs\ namesspace, modify the polling settings of
the name.
D. From the properties of the \\contoso.com\dfs\ namesspace, modify the ordering method of
the name.
Answer: D
QUESTION 179
Your company’s corporate network uses Network Access Protection (NAP).
Users are able to connect to the corporate network remotely.
You need to ensure that data transmissions between remote client computers and the corporate network are as secure as possible.
What should you do?
A. Apply an IPsec NAP policy.
B. Configure a NAP policy for 802.1X wireless connections.
C. Configure VPN connections to use MS-CHAP v2 authentication.
D. Restrict Dynamic Host Configuration Protocol (DHCP) clients by using NAP.
Answer: A
QUESTION 180
You configure a full server backup on a server as shown in the exhibit. (Click the Exhibit button.)
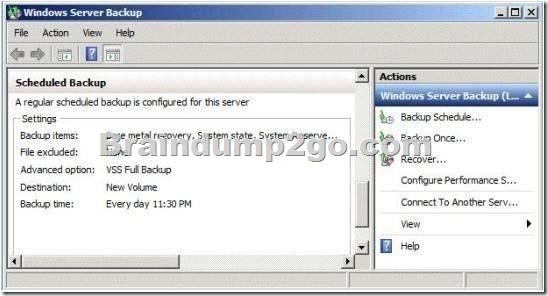
You need to ensure that a full server backup runs each day at 23:45 and that a custom script runs when the backup completes.
Which administrative tool should you use to achieve this task? To answer, select the appropriate tool in the answer area.
![180-1_thumb[1] 180-1_thumb[1]](http://examgod.com/bdimages/16b1e32bb31d_7AEA/180-1_thumb1_thumb.jpg)
Answer:
![180-2_thumb[1] 180-2_thumb[1]](http://examgod.com/bdimages/16b1e32bb31d_7AEA/180-2_thumb1_thumb.jpg)
Want to be 70-642 certified? Using Braindump2go New Released 70-642 Exam Dumps Now! We Promise you a 100% Success Passing Exam 70-642 Or We will return your money back instantly!
http://www.braindump2go.com/70-642.html
Braindump2go 70-642 Dumps PDF Free Download (161-170) Study Latest Braindump2go 70-642 Practice Exam Questions From Today Pass 70-642 Easily! (181-190)
Comments are currently closed.